Splunk has some enormously powerful features for analyzing data. One of the most popular is the ability to take highly analytical information and render it in ways that are understandable by everyone. This feature is referred to as data enrichment. Splunk lookups command enables data enrichment is built into Splunk processing language.
What are Splunk Lookups?
Lookups provide the ability to substitute cryptic information with more readable information without altering the meaning. For example, A successful rendering of a website in a browser can be identified by the HTTP code of 200 or (OK) and an unsuccessful rendering might be a HTTP code of 400 or (Page not found). If you had to create a report on the successful and unsuccessful Web page hits you would not want your audience to ponder; what is the meaning of 200? Or what is the meaning of 400? …while they are reading your report. You can use a Lookup to take the cryptic value of 200 and render the human readable equivalent of (OK).
The Benefits of Splunk Lookups
We examined one of the benefits of lookups, but there are other benefits as well.
Benefit #1
You can use a lookup to provide additional information to a search from a separate file. This is a way to add more valuable information to the search that might appeal to the view of search results.
Benefit #2
Lookups can be used as a way of dynamically filtering events in a search. This provides the ability to filter events based on a list of preset values.
Benefit #3
Lookups can be used to detect events that are not supposed to show up in the data. It is a form of anomaly detection.
Types of Splunk lookups
There are three basic lookup commands in the Splunk Processing Language.
Lookup Command
The lookup command provides match field-value combinations in event data with field-value combination inside an external lookup table file or KV-STORE database table.
Inputlookup Command
The inputlookup command searches the content of a lookup table. The lookup table can be in a CSV file or KV-STORE database table.
Outputlookup Command
The outputlookup command can write information into a CSV file or KV-STORE database table.
How do you use lookups?
Example #1
You can use lookups to provide information to a search that is not currently available in the raw data. Let us say that you have a lookup table that is name “product_info” and it contains the following information:
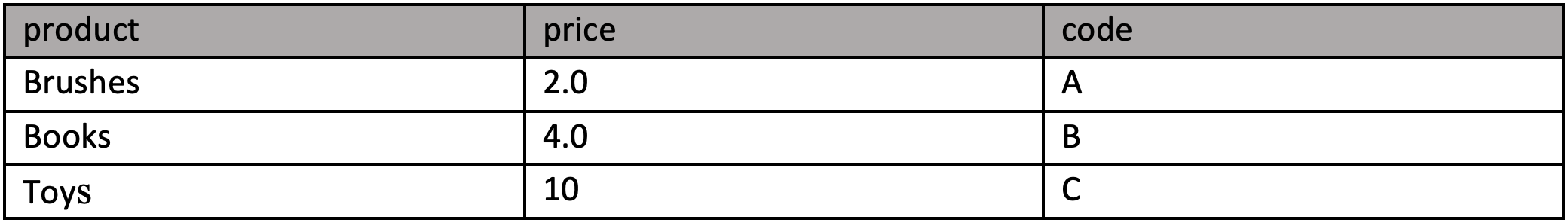
Suppose you want you to provide the product and price in your output results using the Code field values from your raw data in Splunk and you want all the fields to show up in a report. You can add the lookup table to your search like this:
sourcetype vendor | stats count by product_code | lookup product_code OUTPUTNEW product, price.
You can then use a table command to render all the fields in an appropriate format.
Example #2
You can use a lookup to filter events in a more dynamic way. What if you only want to display events that contain certain field values and not others? Then you might use a search like this:
| makeresults | eval code=”b” | search [ inputlookup product_code.csv | fields code].
Example #3
You can use a lookup to find events that are not supposed be in the data. They are called anomalies. To use a look as an anomaly detector the search might look like this:
sourcetype=my_source_events | stats count by events_to_inspect as suspected_anomalies | search NOT [| inputlookup known_match.csv] | table component.
Conclusion
Splunk lookups power offers capability for data enrichment making your search results more human-readable and relevant. Using Splunk lookups for filtering, adding, and tracking information is an excellent feature for making your search more effective and valuable to audiences.
If you found this helpful…
You don’t have to master Splunk by yourself in order to get the most value out of it. Small, day-to-day optimizations of your environment can make all the difference in how you understand and use the data in your Splunk environment to manage all the work on your plate.
Cue Atlas Assessment: Instantly see where your Splunk environment is excelling and opportunities for improvement. From download to results, the whole process takes less than 30 minutes using the button below: