Take a moment ask yourself — how efficient are your searches in Splunk?
One of the biggest advantages of Splunk is the speed of which you get your information back. It’s important to maximize that speed so you, your team, and your company get results faster. Now you’re thinking, “Sure, that’d be great. But I don’t have time to be constantly tweaking my searches.” Thankfully, these tips can help. You can find that quick tune-up on speed just by re-ordering your searches.
Transform your Searches
In SPL, there are numerous search commands you can use to tune-up your Splunk searches. Let’s walk through different types of commands, how they make your Splunk environment more efficient, speed up productivity, and get results faster.
In Splunk, there are different commands types like distributed streaming searches, centralized streaming searches, transforming generating, orchestrating and data set processing. Depending on the order of these command types, you can offload some of the searches into the indexer.
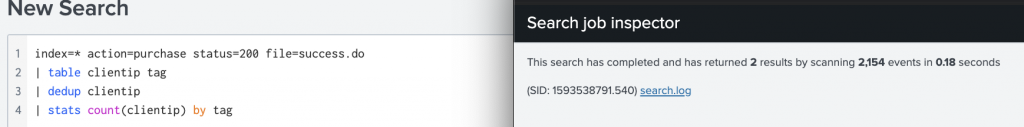
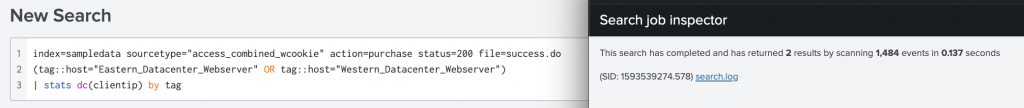
Let’s take a look at an example that demonstrates how the command order can really make a difference:
The No-Good Scenario
Take a streaming command, followed by a non-streaming command, followed by another streaming command. With this lineup, the process flows like this — your data travels from your search heard, down to your indexer, and says, “Hey indexer, I want to know about this stuff.” Your indexer goes “Okay, here’s all your stuff.” Now, the search head dumps all of that “stuff” on the third command, which now has to do all of that work.
The Good Scenario
Take a streaming command, followed by a streaming command, followed by a non-streaming command. In this scenario, you’ve lined up your streaming commands. You can stream data down to the indexer, search for the data you need. Then, use that second streaming command to apply those additional filters, clean up the data, and THEN feed the data back up to the search head. With these small adjustments, you’ve made your data streaming process faster and decreased the network load going back and forth. Now, you have cleaner and more efficient results.
Identify Search Performance
Now that we’ve covered how you can speed up your searches, let’s dig into finding those searches you want to tune-up. Short answer: your job inspector. While any of your current searches are running, you can head into the job inspector and monitor the performance of this search. See below for what to look for in your Splunk job inspector.
From these suggestions, here are two key benefits you can take away from optimizing your Splunk transforming commands:
- Quicker speed of the search. This alleviates some of the human-hours that searches can take. Even just 30 seconds of saved search time can add up over time.
- Make life easier for engineers. We know the role of a Splunk engineer is a demanding one. By optimizing your search commands, you can get results faster and move on to the next item on your very long list.
Make Optimization a Priority
Maybe you’d like to optimize your searches, but frankly, it’s not a top priority on that long list of to-do’s we mentioned earlier. That’s where Kinney Group can jump in and help. At Kinney Group, our Expertise on Demand Service offering does just that (and more). Our engineers have the ability to look through search efficiency, put things in the right order to really optimize your environment, and propose different commands to get different outputs based on best practice. You have the data. We can optimize that data and give you the full picture.





