While the Splunk command rename is an overall simple command, it is an essential one for making dashboards and reports easy for your users to consume. The rename command is used to change the names of fields in search results. This is useful when you want to improve the readability of your Splunk data outputs. Users can make their search results and dashboards more understandable, especially when they are dealing with data fields that have names which are not descriptive enough for your audience to understand. The rename command is an especially useful feature for when you need to organize and clarify data in your Splunk search results and visualizations.
How to Use the rename Command
To use rename, simply insert the command like any other Splunk command, then include the field you want to change, and its new name, as shown in the example below.
index=win*
| eval EventCode=EventCode*50
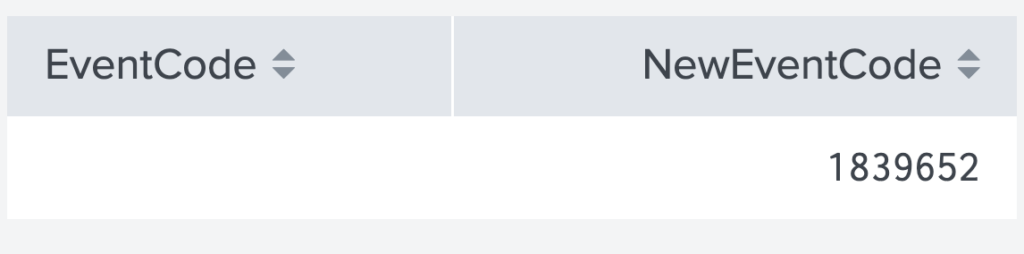
| rename EventCode as NewEventCode
In this example, the field EventCode is now renamed as NewEventCode. As a result of using rename here, the original field name can no longer be used, and any attempts to display it will be met with empty data, as illustrated below.
Using rename Multiple Times in a Single Command
Splunk Users can do multiple renames in a single command, increasing search legibility and decreasing SPL length. Rename also allows users to change field names into longer strings with spaces using double quotes (“). It is important to remember that if you want to reference a field with spaces later, you may need to use double (“) or single (‘) quotes depending on the command.
index=win*
| eval EventCode=EventCode*50
| rename EventCode as NewEventCode logdata as LogData passwords as "Masked Passwords"
A best practice for the rename command is to put it at the very end of a search query. This ensures that while reading long searches, users won’t have to track changes to field names or deal with cumbersome fields with spaces. In most cases, the rename commands should be placed after the last transformation command. You typically place them after your stats, charts, and table commands. Don’t worry though, the rename will still affect your visualizations and tables even if it’s after the command.
For an advanced use case, rename can use wildcards to modify multiple fields at the same time. This is useful for when you are working with data models or fields with common prefixes. For instance, the following search has three fields that get renamed by dropping the ‘pre_’ value from the field name.
| table pre_field_one pre_field_two pre_field_three
| rename pre_* as *
Conclusion
In Splunk, mastering the rename command can significantly streamline your data analysis process. This command is a powerful tool that offers flexibility and efficiency in modifying field names within your search results. Understanding its usage is key to enhancing the readability and interpretability of your data. Here are three important aspects to remember about the rename command:
- Enhances Readability: Improves clarity of field names, making data analysis more user-friendly.
- Flexible Usage: Allows renaming of one or multiple fields, including wildcard use for broader changes.
- Best Practices: Ideally placed at the end of a search query for maximum clarity.